Supreme Court to decide whether geofence warrants are constitutional
Google has urged the justices to strike down the controversial warrants, which can sweep up location data from hundreds of phones near a crime scene.
Real estate investment opportunities
Google has urged the justices to strike down the controversial warrants, which can sweep up location data from hundreds of phones near a crime scene.
The Rust team is happy to announce a new version of Rust, 1.94.0. Rust is a programming language empowering everyone to build reliable and efficient s...
Reports of a "Great British Firewall" are exaggerated. And even if they wanted to, here's why it would be virtually impossible.
Researchers have found that attackers are abusing OAuth to send users from legitimate Microsoft or Google login pages to phishing sites or malware dow...
Google has patched 129 Android vulnerabilities, including an actively exploited flaw in a widely used Qualcomm component.
At the center of the dispute is how far AI models should be allowed to go inside military systems.
Ever since I was using a text editor for R I have been using ESS. That makes it 10 years now. And so, I have decided that it is enough. I started usin...
Latin America's threat landscape is evolving fast — and reactive defense is no longer enough. PIX fraud, ransomware, and targeted attacks are outpacin...
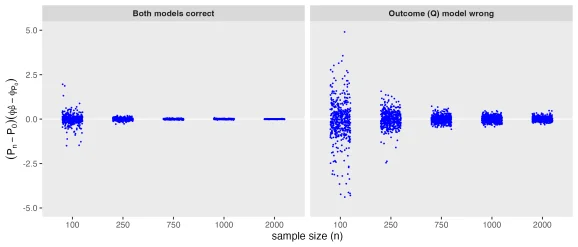
In the previous post, I argued that understanding TMLE starts with understanding how estimation error behaves. In particular, we saw that influence fu...
Two hundred forty-one of the new packages submitted to CRAN in January were still there in mid-February. Here are my Top 40 picks in nineteen categori...

A while ago, I decided to learn some Rust. I bought a book, opened it months later and started a small side-project: porting my R package saperlipopet...

Recorded Future is expanding its payment fraud prevention capabilities through a partnership with CYBERA, the industry leader in detecting and verifyi...

January 2026 saw 23 actively exploited CVEs, including APT28’s Microsoft Office zero-day and critical auth bypass flaws impacting enterprise systems.
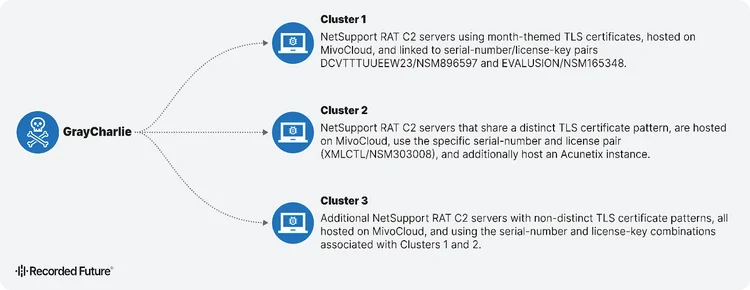
GrayCharlie turns compromised WordPress sites into malware delivery machines. Discover how this threat actor chains fake browser updates and ClickFix...
Learn how network intelligence gives security teams control over threat investigation with global visibility—no more drowning in generic, passive thre...

Discover how Autonomous Threat Operations reduces 27 manual steps to as few as 5 largely automated ones, delivering the speed, scale, and effectivenes...
This article explores how Recorded Future served as Customer Zero for Autonomous Threat Operations, testing the new solution within our own SOC to val...
Time flies! Six months have passed since our last crates.io development update, so it's time for another one. Here's a summary of the most notable cha...

Understand the future of threat and vulnerability management (TVM). Learn what TVM is, why traditional tools fail, and how intelligence is essential i...
This is another post in our series covering what we learned through the Vision Doc process. In our first post, we described the overall approach and w...
Are you sure you want to sign out?