Declaring generative AI use in research and university studies
I often find requests to ‘declare use of generative AI’ frustratingly vague. There’s so many different potential uses. And use can be reported at so m...
Construction industry and development projects
I often find requests to ‘declare use of generative AI’ frustratingly vague. There’s so many different potential uses. And use can be reported at so m...
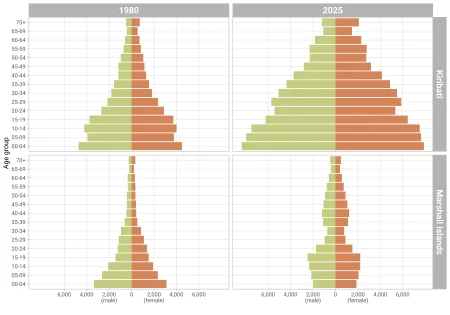
This post is the fifth of a series of seven on population issues in the Pacific, re-generating the charts I used in a keynote speech before the Novemb...
Two hundred forty-one of the new packages submitted to CRAN in January were still there in mid-February. Here are my Top 40 picks in nineteen categori...

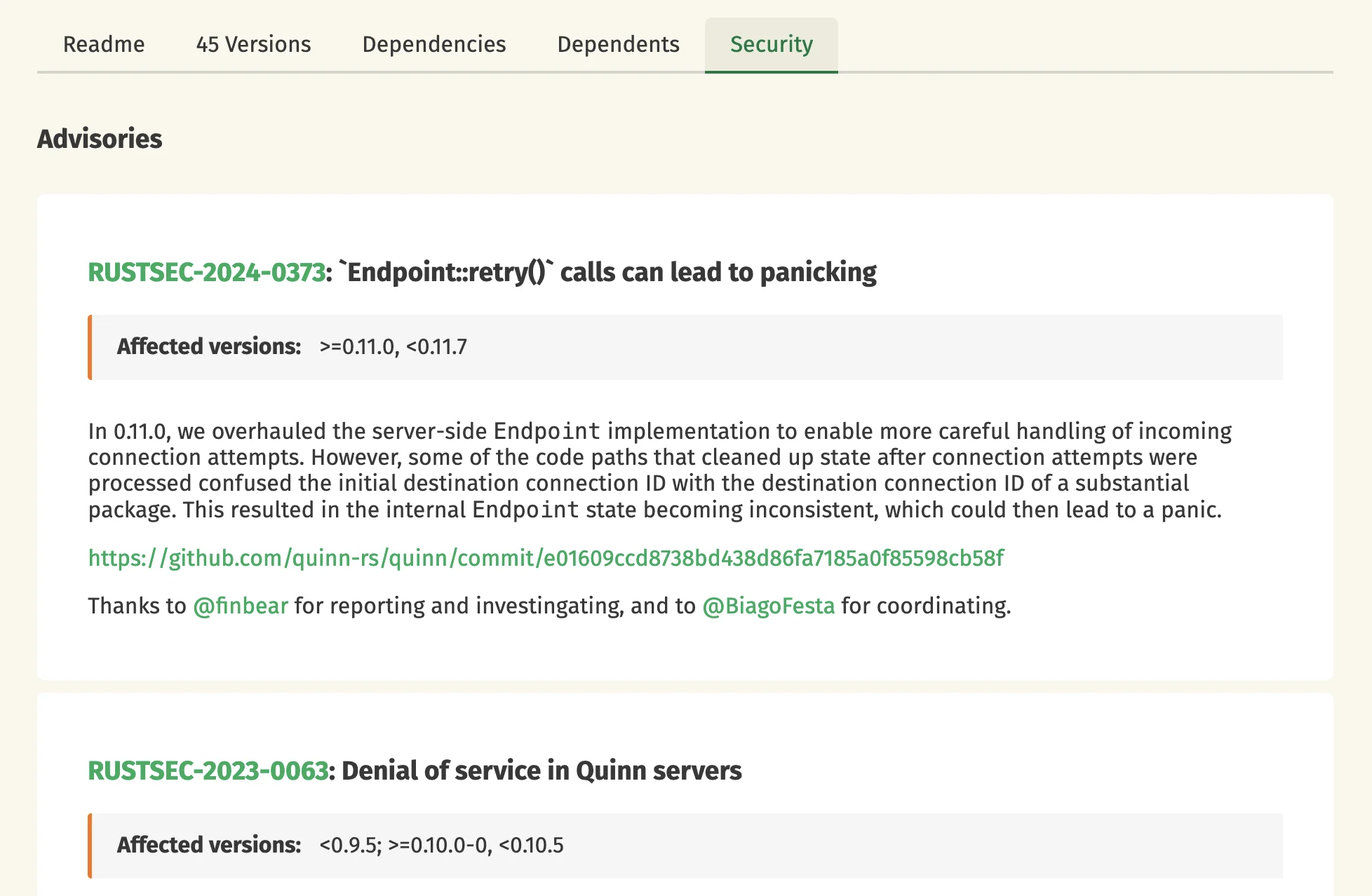
A while ago, I decided to learn some Rust. I bought a book, opened it months later and started a small side-project: porting my R package saperlipopet...

Recorded Future is expanding its payment fraud prevention capabilities through a partnership with CYBERA, the industry leader in detecting and verifyi...
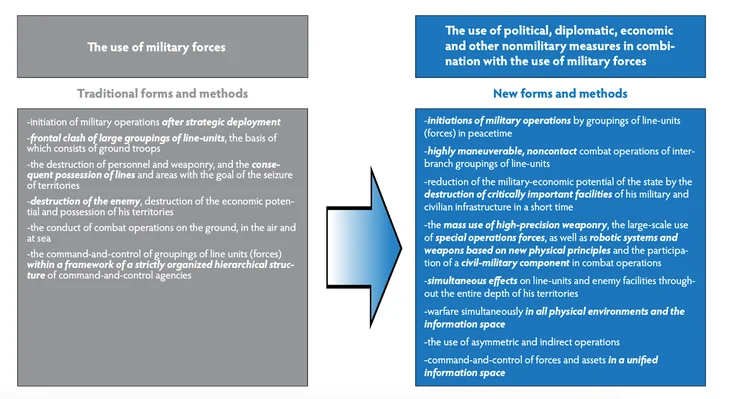
Russia is escalating its hybrid warfare against NATO into a coordinated, full-scale campaign blending cyber attacks, sabotage, and influence operation...

January 2026 saw 23 actively exploited CVEs, including APT28’s Microsoft Office zero-day and critical auth bypass flaws impacting enterprise systems.
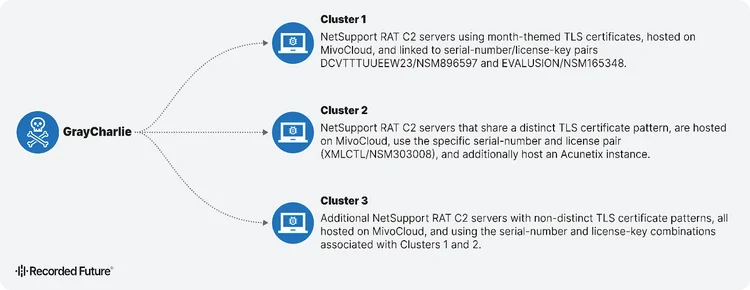
GrayCharlie turns compromised WordPress sites into malware delivery machines. Discover how this threat actor chains fake browser updates and ClickFix...
Learn how network intelligence gives security teams control over threat investigation with global visibility—no more drowning in generic, passive thre...

Discover how Autonomous Threat Operations reduces 27 manual steps to as few as 5 largely automated ones, delivering the speed, scale, and effectivenes...
This article explores how Recorded Future served as Customer Zero for Autonomous Threat Operations, testing the new solution within our own SOC to val...
Time flies! Six months have passed since our last crates.io development update, so it's time for another one. Here's a summary of the most notable cha...

Understand the future of threat and vulnerability management (TVM). Learn what TVM is, why traditional tools fail, and how intelligence is essential i...
This is another post in our series covering what we learned through the Vision Doc process. In our first post, we described the overall approach and w...

Remember the Ashley Madison data breach? That was now more than a decade ago, yet it arguably remains the single most noteworthy data breach of all ti...

December 2025 saw a 120% surge in critical CVEs, with 22 exploited flaws and React2Shell (CVE-2025-55182) dominating threat activity across Meta’s Rea...
Stop ransomware before encryption begins. Learn how intelligence-driven detection tools can help identify precursor behaviors and reduce false positiv...
Threat intelligence practitioners from Global Payments, Adobe, and Superhuman reveal how mature CTI programs transform data overload into strategic bu...
Insikt Group reveals how GRU-linked BlueDelta evolved credential-harvesting campaigns targeting government, energy, and research organizations across...
Ransomware groups made less money in 2025 despite a 47% increase in attacks, driving new tactics: bundled DDoS services, insider recruitment, and gig...
Are you sure you want to sign out?