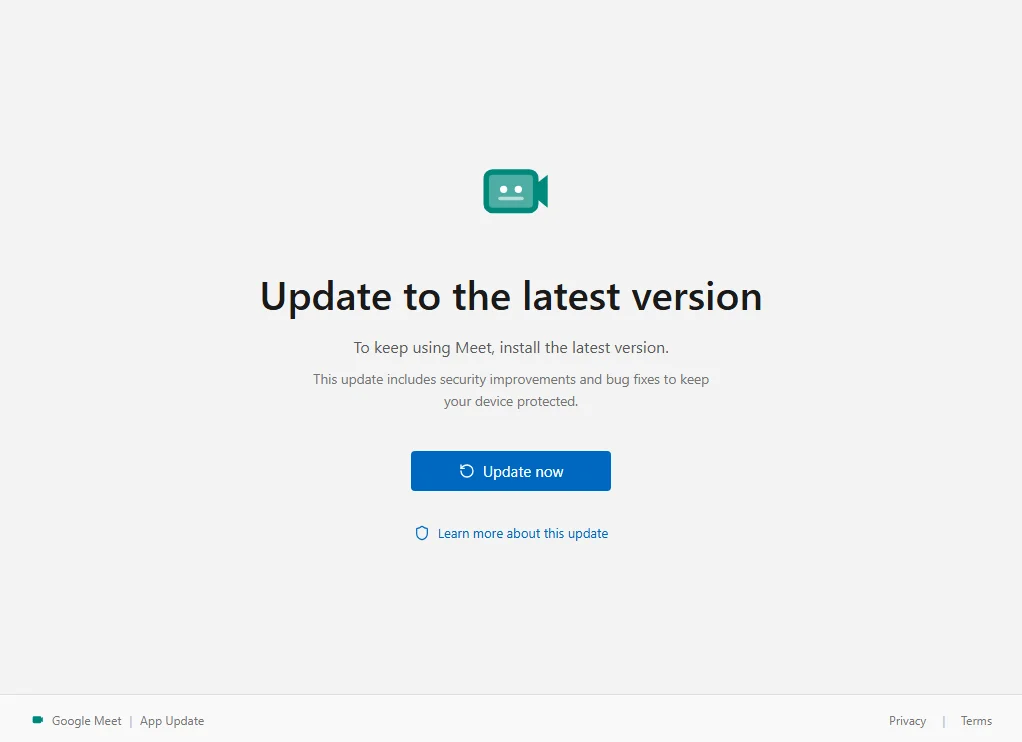
One click on this fake Google Meet update can give attackers control of your PC
We found a fake Google Meet update that enrolls the victim's Windows PC in an attacker's device management system.
We found a fake Google Meet update that enrolls the victim's Windows PC in an attacker's device management system.
This week on the Lock and Code podcast, we speak with Matthew Guariglia about Ring smart doorbells and the surveillance network they create.
The quiz is just bait. The real goal is to win permission to send browser notifications that can later be used for ads, scams, or shady promotions.
Researchers uncovered fake Claude Code install pages spreading infostealers that steal passwords and browser sessions.
A suspected breach of the FBI’s wiretap network has investigators asking whether a nation-state was involved.
Dutch intelligence warns that attackers are hijacking Signal and WhatsApp accounts by tricking users into sharing verification codes or linking a mali...
Google knows a lot about you. Here's how to check your Google Search history and how to prevent future tracking.
Discover how 43% of security leaders now use threat intelligence for strategic planning. Explore key insights from the 2025 State of Threat Intelligen...
Discover how threat intelligence has moved from the SOC to the boardroom. Learn why modern enterprises use it to drive strategic decisions, manage ris...

Explore the latest third-party risk statistics and learn how data-driven, continuous monitoring for third-party risk assessments can protect your supp...
Move beyond noise. Learn how to build effective threat intelligence operations that turn raw data into actionable insights and proactive cyber defense...
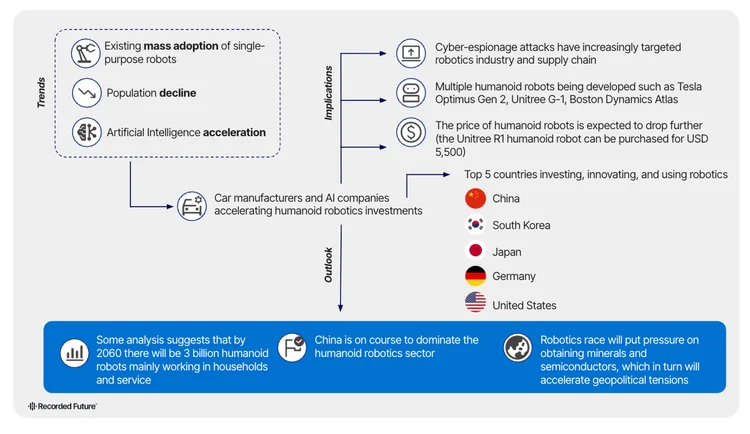
Humanoid robots are arriving faster than anyone expected. Discover the hidden risks, global power shifts, and breakthroughs shaping the future — befor...
Discover how threat intelligence automation from Recorded Future empowers security teams with real-time insights, faster response, and greater efficie...

Evaluating digital risk intelligence platforms? Learn the 5 essential capabilities you should consider in order to protect your brand, assets, and att...

Learn how threat intelligence identifies supply-chain compromise risks in SaaS integrations and how Recorded Future helps organizations defend against...
Are you sure you want to sign out?